
Liang He
I'm an assistant professor at University of Colorado Denver (CU-Denver). My research focuses on cyber-physical systems (CPS) and internet-of-things (IoT), with applications to batteries, vehicles, and industrial control systems. Before joining CU-Denver, I worked as a research fellow at University of Michigan (2015-2017) and Singapore University of Technology & Design (2012-2014). I co-founded Batteries beyond Batteries (BBB).
I'm joining the School of Computing at University of Nebraska Lincoln as an associate professor in Fall 2024. All students at CPSL are either moving together with me or graduated at CU-Denver with award (and a good job)!
Contact Me [CV]
The best way to reach is through my email at: liang.he@ucdenver.edu, or just stop by my office at Lawrence St. Center, LW816.
News and Announcements
-
07/2024One paper is accepted by IEEE TDSC.
-
07/2024One paper is accepted by IEEE TVT.
-
06/2024One paper is accepted by RAID'24.
-
04/2024Congratulations to Adarsh Thoke, who have been awarded the Graduate Education Distinguished Master’s Capstone Award of CU-Denver.
-
04/2024Additional congratulations to Ngoc Que Anh Tran, who have been awarded the 2024 Outstanding Graduates of the Engineering College.
-
04/2024Promotion to associate professor and award of tenure are approved by CU-Denver Board of Regents.
-
04/2024Congratulations to Daniel Rodriguez and Ngoc Que Anh Tran, who have been awarded the 2024 Outstanding Graduates of the CSE Department.
-
3/2024Presented our work at Destination Startup Showcase 2024.
-
3/2024One paper is accepted by IEEE TDSC.
-
2/2024Recieved the Early Career Award for Excellence in Research (CEDC@CU-Devner).
-
1/2024Presented our work at Boulder New Tech.
-
12/2023A book chapter in "AI Embedded Assurance for Cyber Systems" is published by Springer.
-
12/2023Presented our work at University of Cambridge.
-
12/2023Congratulations to Nathan Maas, who has been awarded the 2023 Outstanding Graduate of the CSE Department (BS Category).
-
11/2023Presented our work at University of Michigan.
-
08/2023One proposal is funded by NSF.
-
07/2023Congratulations to Hojun Choi, who has been awarded the Chancellor Scholarship.
-
06/2023V-Health is selected as one of the best paper candidates of ACM e-Energy'23.
-
06/2023One proposal is funded by NSF.
-
06/2023One point-of-view article on battery-enabled cybersecurity management system is accepted by Proceedings of the IEEE.
-
04/2023One proposal is funded by NSF.
-
04/2023Congratulations to John Marinelli, who has been awarded the 2023 Outstanding Graduate of the CSE Department (Graduate Category).
-
02/2023Joined the Advisory Reviewer Board of NETL@DoE.
-
10/2022One paper on reverse engineering PLC code is accepted by ACM SenSys'22.
-
10/2022Joined the editorial board of IEEE Transactions on Vehicular Technology.
-
09/2022Batteries Beyond Batteries is incorporated.
-
09/2022One proposal is funded by NSF.
-
05/2022Congratulations to John Pace, who has been awarded the 2022 Outstanding Graduate of the Engineering College (Graduate Category).
-
05/2022Congratulations to Dennis Mills, who has been awarded the 2022 Outstanding Graduate of the CSE Department (Undergraduate Category).
-
04/2022One proposal is funded by Colorado OEDIT.
-
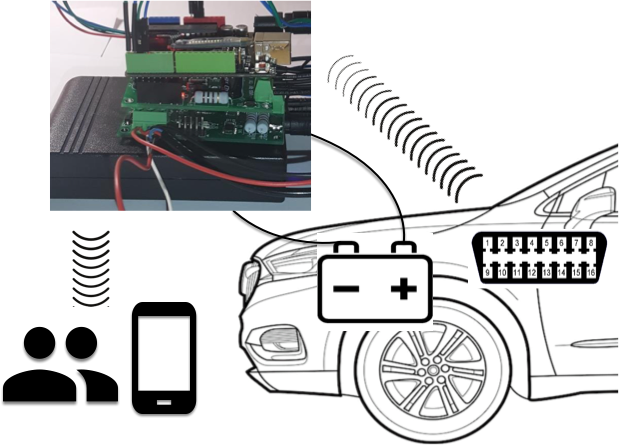
04/2022One paper on vehicle immobilization is accepted by ACM MobiSys'22.
-
03/2022One proposal is funded by NASA.
-
11/2021We won the Lab Venture Challenge 2021!
-
10/2021University Nominee for The Blavatnik National Awards for Young Scientists.
-
10/2021One paper on vehicle diagnostics is accepted by IEEE TMC.
-
04/2021One proposal is funded by NASA.
-
06/2021Received Lewis Family Innovation Award.
-
06/2021Invited paper on batteries-as-sensors is published by ACM GetMobile.
-
02/2021One paper on robot diagnostics is accepted by IEEE TMC.
-
10/2020One paper on driver authentication is accepted by ACM UbiComp'21.
-
10/2020One paper on robot diagnostics is accepted by ACM SenSys'20.
-
08/2020Recieved CRC fellowship from CU-Denver.
-
05/2020One paper on ICS diagnostics is accepted by RAID'20.
-
05/2020Congratulations to Rhys Butler, who has been awarded the Chancellor Scholarship.
-
03/2020One paper on battery management is accepted by ACM MobiSys'20.
-
02/2020One paper on vehicle localization is accepted by ACM/IEEE IPSN'20.
-
02/2020Received the Young Upwardly Mobile Professor Award.
-
02/2020One paper on WiFi fingerprinting is accepted by ACM/IEEE ICCPS'20.
-
01/2020One paper on batteries-as-thermometers is accepted by ACM UbiComp'20.
-
01/2019One paper on battery management is accepted by ACM/IEEE ICCPS'19.
-
11/2018One paper on vehicle diagnostics is accepted by ACM MobiCom'19.
-
10/2018One paper on battery management is accepted by ACM TOSN.
-
01/2018One paper on WiFi fingerprinting is accepted by IEEE TMC.
-
08/2017One proposal is funded by NSF.
-
04/2017One paper on battery management is accepted by ACM MobiSys'17.
-
03/2017One paper on battery management is accepted by IEEE TMC.
-
01/2017One paper on battery management is accepted by ACM/IEEE ICCPS'17.
Honors and Awards
-
2024Early Career Award for Excellence in Research (CEDC@CU-Denver).
-
2023Best Paper Candidates of ACM e-Energy'23.
-
2021University Nominee for The Blavatnik National Awards
-
2021Winner of Lab Venture Challenge 2021 (State of Colorado)
-
2021Lewis Family Innovation Award (CUDenver)
-
2020Young Upwardly Mobile Professor Award (CUDenver)
-
2017Best Poster Award of ACM MobiSys'17
-
2014Best Paper Award of EAI QShine'14
-
2011Best Paper Award of IEEE GlOBECOM'112011Best Paper Award of WCSP'11
Research
My research focues on cyber-physical systems and Internet-of-Things, such as energy/power systems and ground/space vehicles. We exploit methodologies such as physical modeling and data analytics to diagnose/predict/optimize system performance. In the past, I made research contributions to mobile computing as well as wireless communications and networks.
Please click on each project to find more details.
- Cyber-physical and IoT systems
- Mobile computing and systems
- Cognitive battery management
Research Projects
-
Related Publications: B-CSMS@Proc. of IEEE, Bleuth@MobiSys'22, BAuth@UbiComp'21, BaT@UbiComp'20, BDiag@MobiCom'19.
Supported by: NSF-2336145, NSF-2245223 & 2245224, OEDIT-2022-2453.
Media Coverage (non-exclusive): Automotive News, 9NEWS, WXYZ (ABC).
-
Related Publications: ARES@SenSys'22, BDAV@PHM'22, PIDS@SenSys'20, BPM@MobiSys'20, PLC-Sleuth@RAID'20, AuF@ICCPS'20, BDiag@MobiCom'19.
Supported by: NSF-2231759, NSF-2151374, NASA-80NSSC22CA144, NASA-80NSSC21C0356.
-
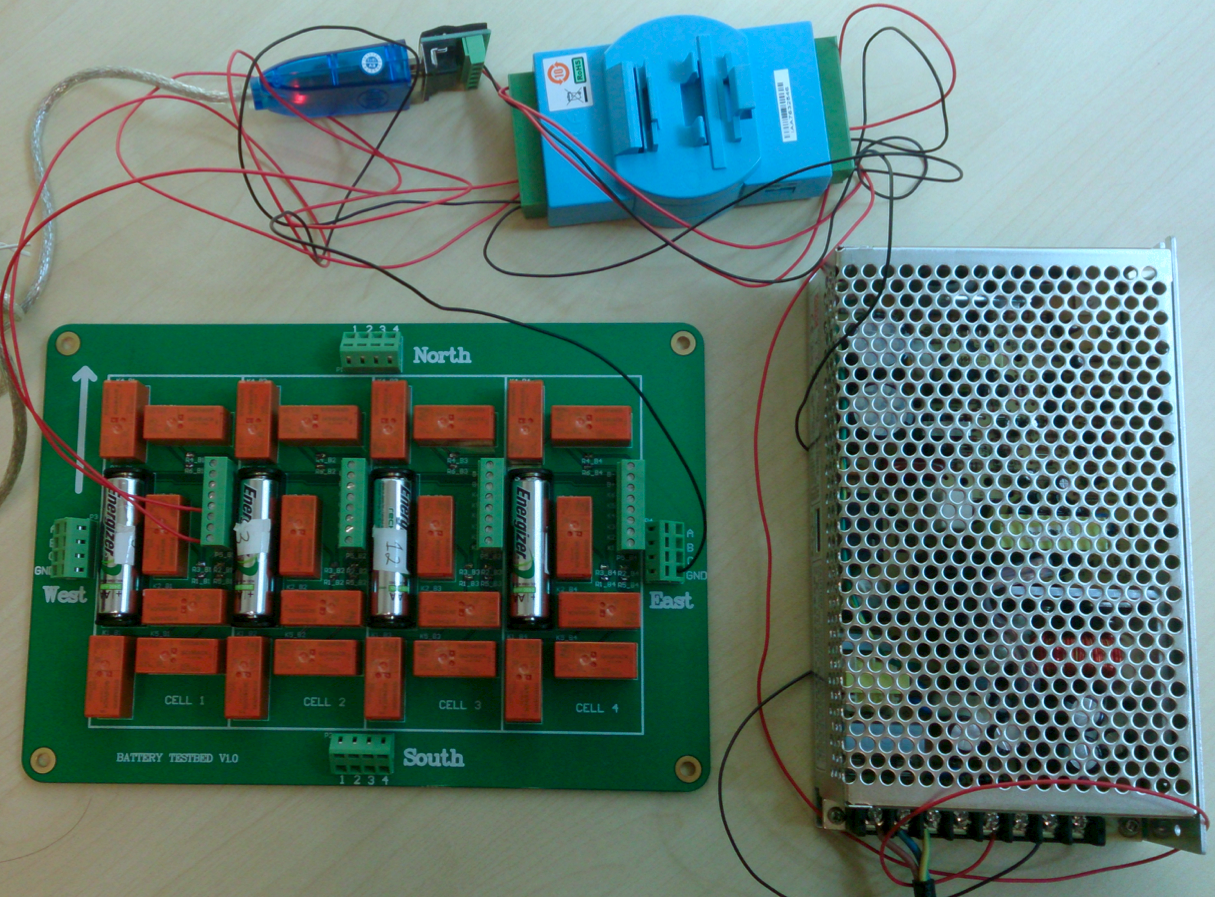
Related Publications: V-Health@e-Energy'23, EA-SoC@ICCPS'19, ChargingDiagnosis@e-Energy'19, iCharge@MobiSys'17, B-BASH@ICCPS'17, *-Aware@ICCPS'16.
Supported by: NSF-1739577.
-
Related Publications: RTSS'16, e-Energy'16, ICCPS'15, ICCPS'14, RTSS'13.
Supported by: NSF-1446117.
Publications
Below is a list of my selected publications.
Filter by type:
Sort by year:
A Reusable Framework for Fault Detection and Isolation in Small Satellites
Conference PapersThe 37th Annual Small Satellite Conference (SmallSat'23), 2023.
Fingerprinting Battery Health Using Relaxing Voltages
Conference PapersThe 14th ACM International Conference on Future Energy Systems (e-Energy'23), 2023.
Reverse Engineering Physical Semantics of PLC Program Variables Using Control Invariants
Conference PapersThe 20th ACM Conference on Embedded Networked Sensor Systems (SenSys'22), 2022.
Unsupervised Anomaly Detection using Batteries in eVTOL Vehicle Propulsion Test Bed
Conference PapersThe 14th Annual Conference of the Prognostics and Health Management Society (PHM’22), 2022.
Battery-Enabled Anti-Theft Vehicle Immobilizer
Conference PapersThe 20th ACM International Conference on Mobile Systems, Applications, and Services (MobiSys'22), 2022.
Authenticating Drivers Using Automotive Batteries
Conference PapersACM International Joint Conference on Pervasive and Ubiquitous Computing (UbiComp'21), 2021.
Detecting Replay Attacks against Industrial Robots via Power Fingerprinting
Conference PapersThe 18th ACM Conference on Embedded Networked Sensor Systems (SenSys'20), 2020.
Mobile Device Batteries as Thermometers
Conference PapersACM International Joint Conference on Pervasive and Ubiquitous Computing (UbiComp'20), 2020.
PLC-Sleuth: Detecting and Localizing PLC Intrusions Using Control Invariants
Conference PapersThe 23rd International Symposium on Research in Attacks, Intrusions and Defenses (RAID'20), 2020.
Causes and Fixes of Unexpected Phone Shutoffs
Conference PapersThe 18th ACM International Conference on Mobile Systems, Applications, and Services (MobiSys'20), 2020.
VLD: Smartphone–assisted Vertical Location Detection for Vehicles in Urban Environments
Conference Papers 2020 ACM/IEEE International Conference on Information Processing in Sensor Networks (IPSN'20), 2020.
Autonomous WiFi Fingerprinting for Indoor Localization
Conference Papers11th ACM/IEEE International Conference on Cyber-Physical Systems (ICCPS'20), 2020.
Online Concurrent Transmissions at LoRa Gateway
Conference PapersIEEE International Conference on Computer Communications (INFOCOM'20), 2020.
Diagnosing Vehicles with Automotive Batteries
Conference PapersThe 25th ACM Annual international Conference on Mobile Computing and Networking (MobiCom'19), 2019.
mLoRa: Multiple Packets Reception Protocol for LoRa Communications
Conference PapersIEEE International Conference on Network Protocols (ICNP'19), 2019.
An Intelligent Phase Identification and Frequency Adjustment Framework for Time-Sensitive Mobile Computing
Conference PapersThe 25th IEEE Real-Time and Embedded Technology and Applications Symposium (RTAS'19), 2019.
Environment-Aware Estimation of Battery State-of-Charge for Mobile Devices
Conference PapersThe 10th ACM/IEEE International Conference on Cyber-Physical Systems (ICCPS'19), 2019.
Adaptive Battery Diagnosis/Prognosis for Efficient Operation.
Conference PapersThe 10th ACM International Conference on Future Energy Systems (e-Energy'19), 2019.
Faulty Location Data Detection in Crowdsourcing: A Compressive Sensing Approach
Conference PapersThe 38th IEEE International Conference on Distributed Computing (ICDCS'18), Vienna, Austria, 2018.
iCharge: User-Interactive Charging of Mobile Devices
Conference PapersThe 15th ACM International Conference on Mobile Systems, Applications, and Services (MobiSys'17), Niagara Falls, NY, USA, 2017.
Mrs.Z: Improving ZigBee Throughput via Multi-Rate Transmission
Conference PapersThe 25th IEEE International Conference on Network Protocols (ICNP'17), Toronto, ON, Canada, 2017.
Battery State-of-Health Estimation for Mobile Devices
Conference PapersThe ACM/IEEE 8th International Conference on Cyber-Physical Systems (ICCPS'17), Pittsburgh, PA, USA, 2017.
Offline Guarantee and Online Management of Power Demand and Supply in Cyber-Physical Systems
Conference PapersThe 37nd IEEE Real-Time Systems Symposium (RTSS'16, CPS Track), Porto, Portugal, 2016.
Resting Weak Cells to Improve Battery Packs' Capacity Delivery via Reconfiguration.
Conference PapersThe 7th ACM International Conference on Future Energy Systems (e-Energy'16), Waterloo, Canada, 2016.
∗-Aware Charging of Lithium-ion Battery Cells
Conference PapersThe ACM/IEEE 7th International Conference on Cyber-Physical Systems (ICCPS'16), Vienna, Austria, 2016.
Privacy-Preserving Compressive Sensing for Crowdsensing based Trajectory Recovery
Conference PapersThe 35th IEEE International Conference on Distributed Computing Systems (ICDCS'15), Columbus, Ohio, USA, 2015.
SHARE: SoH-Aware Reconfiguration to Enhance Deliverable Capacity of Large-Scale Battery Packs
Conference PapersThe ACM/IEEE 6th International Conference on Cyber-Physical Systems (ICCPS'15), Seattle, USA, 2015.
Exploiting Sender-based Link Correlation in Wireless Sensor Networks
Conference PapersThe 22nd IEEE International Conference on Network Protocols (ICNP'14), The Research Triangle, NC, October, 2014.
ESync: An Energy Synchronized Charging Protocol for Rechargeable Wireless Sensor Networks
Conference PapersThe 15th ACM International Symposium on Mobile Ad Hoc Networking and Computing (MobiHoc'14), Philadelphia, PA, USA, 2014.
Reconfiguration-Assisted Charging in Large-Scale Lithium-ion Battery Systems
Conference PapersThe 5th ACM/IEEE International Conference on Cyber-Physical Systems (ICCPS'14), Berlin, Germany, April, 2014.
Mobile-to-Mobile Energy Replenishment in Mission-Critical Robotic Sensor Networks
Conference PapersThe 33rd IEEE International Conference on Computer Communnications (INFOCOM'14) , Toronto, Canada, April, 2014.
A Parallel Identification Protocol for RFID Systems
Conference PapersThe 33rd IEEE International Conference on Computer Communications (INFOCOM'14), Toronto, Canada, April, 2014.
Exploring Adaptive Reconfiguration to Optimize Energy Efficiency in Large-Scale Battery Systems
Conference PapersThe 34nd IEEE Real-Time Systems Symposium (RTSS'13, CPS Track), Vancouver, BC, Canada, December, 2013.
Evaluating Service Disciplines for Mobile Elements in Wireless Ad Hoc Sensor Networks
Conference PapersThe 31st IEEE International Conference on Computer Communications (INFOCOM'12), Orlando, USA, 2012.
Temperature-aware charging strategy for lithium-ion batteries with adaptive current sequences in cold environments.
Journal PaperApplied Energy, Vol. 352, 2023.
Rethink Physical Security: Protecting Vehicles via Battery-enabled Sensing and Control.
Journal PaperProceedings of the IEEE, 2023.
CORMAND2: A Deception Attack against Industrial Robots.
Journal PaperElsevier Engineering, 2023.
R-tracing: Consortium Blockchain-based Vehicle Reputation Management for Resistance to Malicious Attacks and Selfish Behaviors.
Journal PaperIEEE Transactions on Vehicular Technology (TVT), 2022.
Security of Industrial Robots: Vulnerabilities, Attacks, and Mitigations
Journal PaperIEEE Network Magazine, 2022.
Detecting PLC Intrusions Using Control Invariants.
Journal PaperIEEE Internet of Things Journal (IoT-J), 2022
Detecting Engine Anomalies Using Batteries
Journal PaperIEEE Transactions on Mobile Computing (TMC), 2021.
Fingerprinting Movements of Industrial Robots for Replay Attack Detection
Journal PaperIEEE Transactions on Mobile Computing (TMC), 2021.
Using Mobile Device Batteries as Thermometers
Journal PaperACM GetMobile: Mobile Comp. and Comm., 2021.
Power Guarantee for Electric Systems Using Real-Time Scheduling
Journal PaperIEEE Transactions on Parallel and Distributed Systems (TPDS), 2020.
Pinning-Based Switching Control of Cyber-Physical Supercapacitor Energy Storage Systems
Journal PaperIEEE Transactions on Control Systems Technology (TCST), 2019.
An Active Mobile Charging and Data Collection Framework for Clustered Sensor Networks
Journal PaperIEEE Transactions on Vehicular Technology (TVT), Vol. 68, No. 5, pp. 5100-5113, 2019.
PPM: Preamble and Postamble Based Multi-Packet Reception for Green ZigBee Communication
Journal PaperIEEE Transactions on Green Communication and Networking (TGCN), Vol. 3, No. 3, pp. 817-827, 2019.
Multi-Rate Selection in ZigBee
Journal PaperIEEE/ACM Transactions on Networking (ToN), Vol. 27, No. 3, pp. 1055-1068, 2019.
A General Analysis Framework for Soft Real-Time Tasks
Journal PaperIEEE Transactions on Parallel and Distributed Systems (TPDS), Vol. 30, No. 6, pp. 1222-1237, 2019.
Extending Battery System Operation via Adaptive Reconfiguration
Journal PaperACM Transactions on Sensor Networks (TOSN), Vol. 15, No. 11, 2019.
SoH-Aware Charging of Supercapacitors with Energy Efficiency Maximization
Journal PaperIEEE Transactions on Energy Conversion (TEC), Vol. 33, No. 4, 2018.
SoH-Aware Reconfiguration in Battery Packs
Journal PaperIEEE Transactions on Smart Grid (TSG), Vol. 9, No. 4, pp. 3727-3735, 2018.
Low-Overhead WiFi Fingerprinting
Journal PaperIEEE Transactions on Mobile Computing (TMC), Vol. 17, No. 3, pp. 590-603, 2018.
Transmit Power Control for D2D Underlaid Cellular Networks Based on Statistical Features
Journal PaperIEEE Transactions on Vehicular Technology (TVT), Vol. 66, No. 5, pp. 4110-4119, 2017.
A Case Study on Improving Capacity Delivery of Battery Packs via Reconfiguration
Journal PaperACM Transactions on Cyber-Physical Systems (TCPS), Vol. 1, No. 2, Feb. 2017.
Battery-Aware Mobile Data Service
Journal PaperIEEE Transactions on Mobile Computing (TMC), Vol. 16, No. 6, pp. 1544-1558, 2017.
ESync: Energy Synchronized Mobile Charging in Rechargeable Wireless Sensor Networks
Journal PaperIEEE Transactions on Vehicular Technology (TVT), Vol. 65, No. 9, pp. 7415-7431, 2016.
RAC: Reconfiguration-Assisted Charging in Large-Scale Lithium-ion Battery Systems
Journal PaperIEEE Transactions on Smart Grid (TSG), Vol. 7, No. 3, pp. 1420-1429, 2016.
Evaluating the On-Demand Mobile Charging in Wireless Sensor Networks
Journal PaperIEEE Transactions on Mobile Computing (TMC), Vol.14, No. 9, pp. 1861–1875, 2015.
Design of a Mobile Charging Service for Electric Vehicles in an Urban Environment
Journal PaperIEEE Transactions on Intelligent Transportation Systems (TITS). No. 99, pp. 1-12, 2014.
Temperature-Assisted Clock Synchronization and Self-Calibration for Sensor Networks
Journal PaperIEEE Transactions on Wireless Communications (TWC), Vol. 13, No. 6, pp. 3419-3429, 2014.
Opportunistic Flooding in Low-Duty-Cycle Wireless Sensor Networks with Unreliable Links
Journal PaperIEEE Transactions on Computers (TC), Vol. 63, No. 11, pp. 2787-2802, 2014.
Achieving Energy Synchronized Communication in Energy-Harvesting Wireless Sensor Networks
Journal PaperACM Transactions on Embedded Computing Systems (TECS), Vol. 13, No. 68, 2014.
Evaluating Service Disciplines for On-Demand Mobile Data Collection in Sensor Networks
Journal PaperIEEE Transactions on Mobile Computing (TMC), Vol. 13, No. 4, pp. 797-810, 2014.
A Progressive Approach to Reducing Data Collection Latency in Wireless Sensor Networks with Mobile Elements
Journal PaperIEEE Transactions on Mobile Computing (TMC), Vol. 12, No. 7, pp. 1308-1320, 2013.
Demo: Protecting Electric Scooters from Thefts Using Batteries
Demos and postersThe 20th ACM International Conference on Mobile Systems, Applications, and Services (MobiSys'22), 2022.
Poster: Battery-Enabled Vehicle Immobilizer
Demos and postersThe 20th ACM International Conference on Mobile Systems, Applications, and Services (MobiSys'22), 2022.
Diagnosing PLC Using Control Invariants
Demos and postersThe 41th Real-Time Systems Symposium (RTSS'20), 2020.
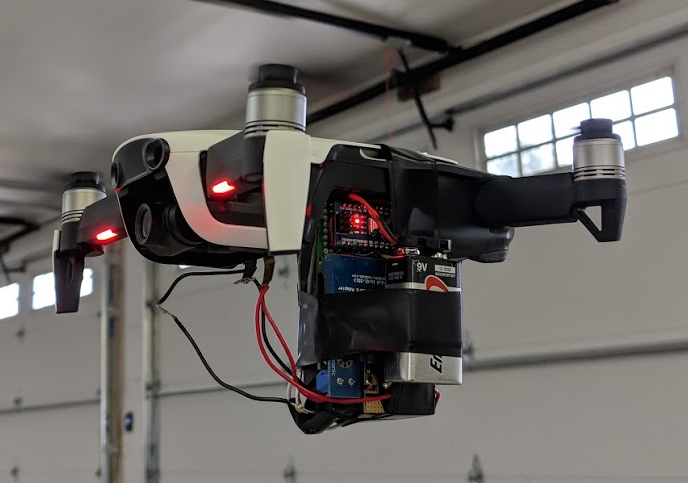
Estimating Altitude of Drones Using Batteries
Demos and postersThe 5th ACM/IEEE Conference on Internet of Things Design and Implementation (IoTDI'20), 2020.
Charge My Phone As I Instruct
Demos and postersThe 15th ACM International Conference on Mobile Systems, Applications, and Services (MobiSys'17), Niagara Falls, NY, USA, 2017.
Robust and undemanding wifi-fingerprint based indoor localization with independent access pointst
Demos and postersProceedings of the Microsoft Indoor Localization Competition (IPSN), Seattle, WA, USA, 2015.
An Energy Synchronized Charging Protocol for Rechargeable Wireless Sensor Networks
Demos and postersIn The 15th ACM International Symposium on Mobile Ad Hoc Networking and Computing (MobiHoc'14), Philadelphia, PA, USA, 2014.
Reconfiguration-based Energy Optimization in Battery Systems: a Testbed Prototype
Demos and postersIn The 34nd IEEE Real-Time Systems Symposium (RTSS'13), Vancouver, Canada, December, 2013.
Exploring Smartphone-based Participatory Computing to Improve Pervasive Surveillance
Demos and postersIn the 11th ACM Conference on Embedded Networked Sensor System (SenSys'13), Rome, Italy, November, 2013.
Energy Synchronized Charging in Sensor Networks
Demos and postersThe 10th ACM Conference on Embedded Networked Sensor Systems (SenSys'12), Toronto, Canada, 2012.
Teaching
I'm teaching the following courses regularly at CSE@CU-Denver.
-
CSCI 3515: Internet-of-Things: Sensing, Communication, and Control
This course focuses on the design, implementation, and testing of end-to-end IoT applications. You can also view this as an advanced version of CSCI 3511. The IoT applications we will discuss include, but not limited to, temperature monitor \& logger, fuel gauge of batteries, step counter, power-line communication system, and so forth.
-
CSCI 5575: Cyber-Physical Systems
This course introduces the basic concepts of cyber-physcial systems and their applications in different domains. This course is designed as research-oriented, involving extensive discussions on existing or new research projects and concepts. The good thing is most of the dicussions are open-ended and there may not exist a correct/wrong answer.
-
CSCI 5800: Battery Management Systems
This course prepares for the era of Zero Emission Vehicles by introducing the core functions of battery management systems and the common practices on how these functions are implemented. Hands-on labs on each of the main functions of battery management systems are designed and integrated in this course.
Students
I work closely with students of cross-discipline backgrounds at CU Denver.
Graduate Research Assistants
-
- Hojun Choi, CSE, since 2023 (Chancellor Scholarship 2023)
- Matthew Michaelis, CSE, since 2023 (EL of our NSF I-Corps team)
- Adarsh Thoke, CSE, since 2023
- Noorul Husssain Shaik, CSE, 2023
- John Marinelli, CSE, 2022-2023 (Outstanding Graduate of CSE Department)
- Keshav Miglani, CSE, 2022
- Samuel Wozinski, CSE, 2021-2022
- John Pace, CSE, 2020-2022 (Outstanding Graduate of Engineering College)
- Yiqin Wang, CSE, 2020-2021
- Debajit Kumar Sandilya, CSE, 2018-2020
- Aishwarya Mulkalwar, CSE, 2018-2019
Undergraduate Research Assistants
-
- Ngoc Que Anh Tran, CSE, 2023-2024 (Outstanding Graduate of CSE Department)
- Daniel Rodriguez, CSE, 2023-2024 (Outstanding Graduate of CSE Department)
- Nathan Maas, CSE, since 2023 (Outstanding Graduate of CSE Department)
- Dennis Mills, CSE, Spring 2022 (Outstanding Graduate of CSE Department)
- John Pace, CSE, 2019-2020
- Andrew Gras, EE, 2018-2019
- Zachary Nye, EE, 2019
- Kevin Macfarlane, CSE, 2018-2019
- Devin Piner, CSE, 2018-2019
- Aaron Zapiler, ME, 2018
Professional Services
TPC Member
-
- 2022: e-Energy, VTC, ICPADS
- 2021: IoTDI, VTC, ICPADS
- 2020: RTCSA, ICCCN, MASS
- 2019: ICPADS, MASS, WCNC, ICNC, ICC, ICCCN, ICME, RCAR, EWSN-Poster
- 2018: ICCPS, GLOBECOM, ICNC, DSCT, VTC2018-Spring, VTC2018-Fall, ICC, MiSeNet, SNTA, WASA, CYBER
- 2017: GLOBECOM, RTAS-Demo, ICC, NAS, ICNC, MiSeNet, GLOBECOM-CQRM, NaNA, ICCC Workshops
- 2016: GLOBECOM, ICNC, NaNA, ICCVE
- 2015: ICNC, ICCVE, ICCC, IoT, E2IoT
- 2014: VTC2014-Fall, WCSP, ICNC, QShine, ICCC, IoT, ICCVE
- 2013: GLOBECOM, WCSP, ICNC, ICCC, ICCVE
- 2012: WiSARN 2012-Spring
Organizing Committee Membership
-
- Regional Program Chair, The 8th Annual IEEE Int. Conf. on CYBER Technology in Automation, Control, and Intelligent Systems (IEEE-CYBER 2018)
- Publicity Co-Chair, The 7th International Workshop on Wireless Sensor, Actuator and Robot Networks (WiSARN 2013-SPRING)
- Publicity Co-Chair, The 6th International Workshop on Wireless Sensor, Actuator and Robot Networks (WiSARN 2012-Fall)
Editorship
-
- Guest Editor: Concurrency and Computation: Practice and Experience
Notes to Prospective Students
- We publish papers, but papers are by no means the most important outcomes of your training or research.
- The #1 technical skill you want to master is the ability to identify and solve a problem that excites both yourself and others. For use/application-driven research, it would be even more advantageous if the problem holds practical value.
- Even more important than the technical skills, the primary objective of your training is to develop the capacity to optimistically navigate an immensely stressful process, such as a PhD, and derive enjoyment from it.
- To successfully undertake the training outlined in items 2 and 3, you must be motivated to push your boundaries by submitting your best work to the most competitive venues for potential publication, and then we circle back to item 1.
- Researchers often collaborate, but it's crucial for students to be trained in a way that equips them to independently complete a project.
CPS Seminar Series
We have been organizing a seminar series on Cyber-Physical Systems with speakers from both academia and industry.
We are sorry to annouce that the seminar by Mr. James Yao from SAP has to be cancelled due to COVID-19. We expect to resume the seminars as soon as things are back to normal.
-
2019 09/30
Toward Human-Transportation Interaction with Ubiquitous Sensing and Applied Machine Learning
Dr. Dongyao Chen, University of Michigan at Ann Arbor
Abstract: As the transportation ecosystem, e.g., vehicles, road infrastructures, becomes increasingly smarter, systems that can enhance the interaction between humans and transportation systems are of paramount importance to road safety and efficiency. Meanwhile, ubiquitous computing devices, such as smartphones and wearables, are empowered by ever-increasing sensing and communication capabilities. Although many existing applications have attempted to harvest the ubiquitous sensory data for facilitating transportation applications, e.g., navigation apps, they are often risk-prone, coarse-grained, and for special purposes. This talk will cover two representative studies that are designed for improving the safety and efficiency of the transportation ecosystem in a scalable and efficient manner. First, I will introduce VSense, a real-time data analytics pipeline for detecting a vehicle’s steering maneuver (i.e., left/right turn and lane change) only with commodity smartphone sensors. Second, I will present TurnsMap, a crowdsensing framework for analysis of risks at intersections. TurnsMap demonstrates a ubiquitous sensing + machine learning framework that is adaptive to numerous smart transportation applications/.
-
2019 04/22
Security and Privacy of Tomorrow’s Connected Vehicles
Mr. Mert Dieter Pese, University of Michigan at Ann Arbor
Abstract: Modern connected and autonomous vehicles (CAVs) are equipped with an increasing number of Electronic Control Units (ECUs) that produce large amounts of data. The data is exchanged between ECUs via an in-vehicle network. Furthermore, CAVs do not only have physical interfaces, but also increased data connectivity to the Internet via their Telematic Control Units (TCUs) which make them accessible remotely just like mobile phones. As a result, an increasing number of attack vectors make vehicles an attractive target for hackers. Automotive cyber-security research is a relatively novel field which tries to respond to constantly rising threats with countermeasures. In this talk, we will give a primer on cyber-security in the automotive domain as well as discuss privacy concerns of the big data generated by cars.
-
2019 04/19
Cyber-Physical Systems for Smart Cities: a Mobility Perspective
Dr. Desheng Zhang, Rutgers University
Abstract: For the first time ever, we have more people living in urban areas than in rural areas. Based on this inevitable urbanization, the research in my group is aimed at addressing sustainability challenges related to urban mobility (e.g., energy consumption and traffic congestion) by data-driven modeling and applications with a Cyber-Physical-Systems (CPS) approach in the vision of Smart Cities. In this talk, I will focus on mobility modeling and resultant applications based on large-scale cross-domain CPS, e.g., cellular networks, payment systems, social networks, and transportation systems (including electric vehicles, taxis, buses, subway, private vehicles, Ubers). I will first show how cross-domain CPS systems can be collaboratively utilized to capture real-time urban mobility by a set of model integration techniques. Then I will show how the captured mobility can be used to design various urban mobile services to close the “loop”, from urban-scale ridesharing to for-hire vehicle dispatching, electric toll collection management, electric-vehicle charging recommendation, and emergency response under mobility anomaly. Finally, I will present some research challenges related to future cross- domain CPS in the context of the smart cities research.
-
2018 10/19
Self-organizing UAV Networks for Providing On-demand Sensing and LTE Connectivity to First Responders
Dr. Eugene Chai, NEC Lab America
Abstract: Autonomous multi-UAV networks will revolutionize the design of systems solutions for civil, entertainment, public services, security and other critical application areas. At NEC Labs, we are particularly interested in the application of such multi-UAV networks to public safety networks. Our goal is simple: how do we design, implement and deploy a reliable and flexible multi-UAV network that can meet the demands of first-responder networks? In this talk, I will introduce SkyLiTE, our multi-UAV network that is designed for public safety applications. SkyLiTE is one of the first efforts at a fully autonomous, untethered multi-UAV network that can be deployed on demand in challenging scenarios to achieve public safety mission objectives. Our SkyLiTE prototype consists of three important components: SkyHAUL, which is a high bandwidth, millimeter wave backhaul network that achieves 1Gbps of bandwidth across the entire multi-UAV network; SkyCORE, a UAV-optimized, lightweight LTE Evolved Packet Core network; and SkyRAN, a full-fledged LTE radio access network. SkyLiTE is deployed either to complement and augment existing terrestrial cellular networks in public safety scenarios, or as a standalone LTE network in areas not covered by fixed infrastructure.
-
2018 08/31
All Your GPS Are Belong To Us: Towards Stealthy Manipulation of Road Navigation Systems
Dr. Yuanchao Shu, Microsoft Research
Abstract: Mobile navigation services are used by billions of users around globe today. While GPS spoofing is a known threat, it is not yet clear if spoofing attacks can truly manipulate road navigation systems. In this work, we explore the feasibility of a stealthy manipulation attack against road navigation systems. The goal is to trigger the fake turn-by-turn navigation to guide the victim to a wrong destination without being noticed. Our key idea is to slightly shift the GPS location so that the fake navigation route matches the shape of the actual roads and trigger physically possible instructions. To demonstrate the feasibility, we perform controlled measurements by implementing a portable GPS spoofer and testing on real cars. The complete attack is validated by extensive trace-driven simulation and real-world driving tests. Deceptive user studies using a driving simulator also show that 95% of the participants follow the navigation to the wrong destination without recognizing the attack.
-
2018 04/09
Addressing Architecture Challenges for Real-Time Vision Processing in Automated Driving Systems
Dr. Shige Wang, General Motors
Abstract: Vision processing is a key component in automated driving systems. Most vision processing algorithms today, however, are not designed for safety-critical real-time applications. Considering these algorithms are typically both data- and computation-intensive and require advanced hardware platform, applying them to automated driving brings new architecture challenges. In this talk, I will discuss some architecture challenges and potential solutions to support the vision processing for real-time vehicle controls.
-
2018 02/12
Predictable GPGPU Computing in Safety-Critical Cyber-Physical Systems
Dr. Cong Liu, University of Texas at Dallas
Abstract: Graphic processing units (GPUs) have seen wide-spread use in several computing domains as they have the power to enable orders of magnitude faster and more energy-efficient execution of many applications. Unfortunately, it is not straightforward to reliably adopt GPUs in many safety-critical cyber-physical systems that require predictable timing correctness, one of the most important tenets in certification required for such systems. A key example is the advanced automotive system where timeliness of computations is an essential requirement of correctness due to the interaction with the physical world. In this talk, I will describe several system-level and algorithmic challenges and our developed solutions on ensuring predictable timing correctness in GPU-accelerated systems.
-
2018 01/29
Emerging Threats in the Mobile Ecosystem
Abstract: During the past decade, we are moving swiftly towards a mobile-centered world. This thriving mobile ecosystem builds upon the interplay of three important parties: the mobile user, OS, and app. These parties interact via designated interfaces many of which are newly invented for or introduced to the mobile platform. Nevertheless, as these new ways of interactions arise in the mobile ecosystem, what is enabled by these communication interfaces often violates the expectations of the communicating parties. This shakes the foundation of the mobile ecosystem and results in significant security and privacy hazards. In this talk, we describe our attempts to fill this gap by: 1.) securing the conversations between trusted parties, 2.) regulating the interactions between partially trusted parties, and 3.) defending the communications between untrusted parties. First, we deal with the case of two opposing parties, mobile OS and app, and analyze the Inter-Process Communication protocol (Binder) between them. We found that the OS is frequently making unrealistic assumptions on the validity (sanity) of transactions from apps, thus creating significant security hazards. We analyzed the root cause of this emerging attack surface and secured this interface by developing effective precautionary testing framework and runtime diagnostic tool. Then, we study the deficiency of how existing mobile user interact with app, a party he can only partially trust. We found that in the current mobile ecosystem, information about the same user in different apps can be easily shared and aggregated, which clearly violates the conditional trust mobile user has on each app. We address this issue by providing an OS-level extension that allows the user to track and control, during runtime, the potential flow of his information across apps. Last, we elaborate on how to secure the voice interaction channel between two trusted parties, mobile user and OS. The open nature of the voice channel makes applications that depend on voice interactions, such as voice assistants, difficult to secure and exposed to various attacks. We solve this problem by proposing the first system that provides continuous and usable authentication for voice commands. It takes advantage of the neck-surface acceleration to filter only those commands that originate from the voice of the owner.